Fraud Article
Fraud rings don’t start with payments, they start with identities
Fraud doesn’t start with money — it starts with identity. Criminal rings scale their attacks by stealing and weaponizing “people,” long before a transaction ever happens. Stop the identity, and you stop the fraud at its source.
When we think about fraud, we often picture the final act: the drained bank account, the unauthorized credit card charge, or the massive chargeback hitting a merchant’s bottom line. We fixate on the money leaving the building. But by the time a transaction alert triggers, the damage is already done. The real crime happened days, weeks, or even months earlier.
The genesis of modern fraud rings isn’t financial, it’s existential. It starts with a stolen identity.
Sophisticated criminal organizations understand that money is just the output; identity is the input. To scale their operations, they don’t just need stolen credit cards; they need the “people” to use them. This shift in tactics has turned identity verification into the critical battleground for fraud prevention. If you can stop the fake or compromised identity at the door, you don’t just stop a transaction; you dismantle the ring.
The raw materials: How identities are compromised
Before a fraud ring launches an attack on a fintech platform or a marketplace, they need fuel. That fuel comes in the form of legitimate user data. The path from a real person to a tool for criminals usually begins with two primary vectors: credential stuffing and malware.
Credential stuffing: The brute force approach
Credential stuffing is the digital equivalent of trying every key on a keyring until one turns the lock. Because so many users recycle passwords across multiple sites, a breach at a low-security forum can compromise a high-security banking login. Fraudsters use automated bots to test millions of stolen username/password pairs against high-value targets.
When a match is found, they don’t just empty the account immediately. They often “incubate” the account, learning the user’s behavior, or sell the validated credentials on the dark web to specialized fraud rings looking for aged, legitimate accounts to launder money.
Malware: The silent observer
Malware provides a more insidious route. Info-stealers and Remote Access Trojans (RATs) infect a user’s device, silently siphoning off cookies, session tokens, and saved passwords. This allows fraudsters to bypass multi-factor authentication (MFA) by mimicking the user’s actual device and digital fingerprint.
Once they control the digital identity, the fraud ring possesses something far more valuable than a credit card number: they have a “mule” persona that looks, acts, and verifies like a real citizen.
Get your free access to the report
Explore the latest insights into digital fraud trends with the Future of Payments Report.
The lifecycle of a zombie identity
Once a fraud ring controls a set of compromised identities, they don’t limit themselves to a single industry. They maximize the return on investment (ROI) for every stolen profile. A single compromised identity often lives a triple life across different sectors, creating a tangled web of fraudulent activity.
1. The fintech beachhead
The journey often starts in fintech. Fraudsters use the stolen identity (or a synthetic one built from stolen parts) to open “drop” accounts. These are valid bank accounts used to receive and move illicit funds. Because the identity belongs to a real person with a credit history, it passes initial automated checks. These accounts become the plumbing for the entire fraud operation.
2. The crypto laundromat
To obscure the money trail, the identity moves to the crypto sector. The fraud ring opens accounts on exchanges to convert fiat currency from the fintech drop accounts into cryptocurrency. This “layering” stage makes the funds nearly impossible to trace. The strict KYC (Know Your Customer) requirements in crypto are hurdles, but armed with high-quality stolen documents and deepfake technology, rings are increasingly successful at scaling these walls.
3. The marketplace exploitation
Finally, the identity hits marketplaces and gig economy platforms. Here, the goal might be different. They might create fake seller accounts to scam buyers, or fake buyer accounts to defraud merchants. In gig economy scenarios, they might set up fake driver or courier accounts to facilitate other crimes or simply to farm referral bonuses and incentives.
This cross-sector pollination is why siloed fraud prevention fails. A “customer” who looks risky to a crypto exchange might look perfectly fine to a ride-sharing app, even though it is the same bad actor pulling the strings.
These tactics—credential stuffing, malware exploitation, and synthetic identity creation—are not theoretical; they converge in real-world attacks like the one uncovered on a major marketplace platform, where seemingly legitimate users masked coordinated criminal operations.
Case study: Dismantling a fraud ring on a marketplace platform
At Veriff, we don’t just verify documents; we look for the subtle connections that reveal organized crime. A recent investigation into an attack on one of our marketplace customers perfectly illustrates how fraud rings operate—and how they can be taken down.
The “Ghost” in the machine
In late 2025, we detected an anomaly during a routine check of a verification. While reviewing session media, a Veriff Verification Specialist noticed the end-user’s video appeared normal, but additional background footage captured a reflection of an unauthorized third party—acting as a handler. This was not a technical glitch, but evidence of orchestrated fraud.
The investigation
The investigation uncovered a sophisticated collusion scheme: legitimate individuals served as fronts, while third-party facilitators directed the onboarding process from behind the scenes. Device and network intelligence revealed the scale and sophistication of the operation, exposing multiple sessions tied to the same devices despite representing different users.
The takedown
The fraud team identified over 500 accounts linked to this fraudulent activity. To neutralize the threat, we deployed a fraud logic to instantly reject any future sessions exhibiting this behaviour. We also shared actionable intelligence with the customer, enabling them to proactively block compromised accounts before they could pose real-world risks.
This case underscores Veriff’s ability to detect, analyze, and disrupt organized fraud through behavioral insight, technical forensics, and rapid, scalable intervention.
The importance of KYC and KYB in fraud prevention
This customer case proves that identity verification is not just a compliance checkbox, it is the primary firewall against organized crime.
When we talk about KYC (Know Your Customer) and KYB (Know Your Business), we often talk about regulations. But in the context of fraud rings, these processes are about disruption.
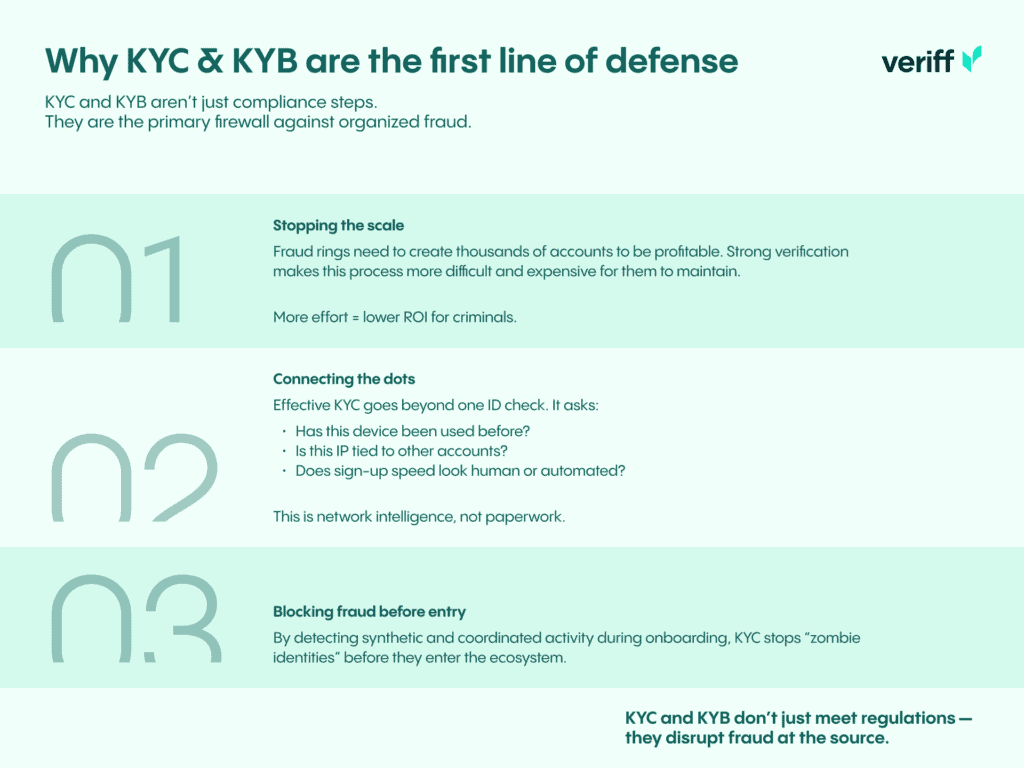
Fraud rings rely on volume. They need hundreds or thousands of active accounts to make their economics work. Robust KYC introduces friction that kills this scalability. If a fraudster needs 15 minutes and a unique device to spoof a single verification, their ROI plummets.
Effective KYC isn’t just about looking at one ID card in a vacuum. It’s about network analysis. It’s about asking:
- Has this device been seen before?
- Is this IP address associated with other “different” users?
- Does the velocity of sign-ups match human behavior, or bot behavior?
By analyzing these signals during the onboarding phase, we prevent the “zombie identity” from ever entering the ecosystem.
Conclusion
The battle against fraud is shifting upstream. We can no longer wait for the chargeback to tell us we have a problem. By the time the money moves, the fraudsters have already won.
To defeat fraud rings, businesses must embed proactive identity intelligence into their onboarding and monitoring systems. This means adopting AI-driven anomaly detection to spot subtle behavioral deviations, implementing robust device and network fingerprinting, and participating in cross-platform intelligence sharing to expose hidden links between seemingly unrelated accounts. By treating identity verification not just as a compliance requirement but as a strategic defense layer, organizations can disrupt fraud rings at inception – before a single transaction is made.

