Fraud Article
Deep dive: How to prevent accound takeovers in digital banking [2026]
Account takeover fraud can cause serious problems, making it difficult for customers to reclaim their accounts without suffering a financial loss. To make matters worse, the relationship between the customer and the business could be irrevocably damaged.
I recall the first time I had to explain to an executive how a customer’s entire banking relationship could be compromised in a matter of hours. This wasn’t a hypothetical scenario; it was a real account takeover. It started with a reused password and escalated to unauthorized transfers totaling tens of thousands of dollars. Recent account takeover fraud statistics from Veriff´s Fraud Report 2026 confirm this was not an isolated incide nt, but part of a broader global threat: in 2025, the net fraud rate across digital verification flows remained above 4% — meaning one in every 25 identity verification attempts was fraudulent — and impersonation fraud accounted for over 85% of all fraud attempts, underscoring how determined attackers are at commandeering digital identities.
That experience crystallized for me how urgent — and personal — the problem of account takeover in digital banking has become. It also explains why financial services leaders in the U.S., U.K., Brazil, Mexico, and Colombia must act now to protect customers and institutions alike.
Account takeover (ATO) is one of the most serious and fast-growing threats in digital banking. It occurs when a fraudster gains unauthorized access to a customer’s online banking account — typically through stolen credentials, phishing, malware, or exploiting weak authentication. Once inside, attackers can transfer funds, alter account details, open new products, or commit additional identity fraud — often before the customer or bank notices. According to the latest Veriff fraud data, sophisticated fraud tactics — including AI-generated media and impersonation techniques — are increasing rapidly, making traditional defenses insufficient on their own.
What is account takeover, and why does it matter?
When I say, ‘what is account takeover?’, I am referring to more than just a stolen username and password. ATO in banking is a multi-stage attack lifecycle: fraudsters harvest credentials or impersonation data, validate access, escalate control (for example by changing communication or authentication channels), and monetize the account through transfers, purchases, or social engineering to support broader identity fraud schemes. The damage is both financial and reputational – customers lose money, banks absorb liability, and trust erodes. The regulatory and compliance consequences can be equally damaging, especially as regulators tighten expectations for strong customer authentication and fraud detection.
Common attack vectors: how fraudsters break in
Understanding how attackers operate is the first step to preventing ATO. In my work I see three vectors repeatedly:
1. Phishing and social engineering. Attackers trick customers into revealing credentials or one-time codes via convincing fake sites or messages. Phishing remains one of the most effective initial access techniques because humans are, inevitably, the weakest link in any security chain.
2. Credential stuffing and password reuse. When credentials leaked from one breach are tried en masse against bank login pages, attackers succeed wherever passwords are reused. Credential stuffing is automated and scalable, making it a high-volume threat for digital banking platforms.
3. Malware and device compromise. Malware on a customer’s phone or PC can capture credentials, intercept SMS-based multi-factor authentication (MFA) codes, or hijack sessions. Mobile banking adoption increases the attack surface, especially in markets where device security practices vary widely.

Fraud is no longer opportunistic — it’s organized and increasingly technology-driven. In 2025, over 4% of all verification attempts were fraudulent, and more than 85% of those involved impersonation. That tells us attackers are doubling down on identity-based attacks, using increasingly sophisticated tools to take over accounts and exploit trust at scale.

Why digital banks and customers are uniquely at risk
Digital banking accounts are high-value targets: they provide direct access to funds, payment rails, credit lines, and sensitive personal information that can be used for identity theft. From the bank’s perspective, ATO can lead to immediate financial losses through reimbursements and chargebacks, longer-term operational costs for investigations and remediation, and regulatory penalties when consumer protections are deemed insufficient.
For customers, the consequences extend beyond drained balances. Attackers can create synthetic identities, apply for new credit in the victim’s name, or lock customers out of critical services. The emotional cost – loss of confidence and time-consuming recovery – can be significant and long-lasting.
How account takeover fraud unfolds in practice
Let me walk you through a typical ATO scenario I’ve seen dozens of times:
First, attackers obtain credentials via a third-party breach. They feed those credentials into automated tools to test login pages (credential stuffing). Where MFA is weak or SMS-based, attackers may intercept codes or trick call-center staff into resetting credentials (social engineering). Once they have control, they change contact details, set up new payment beneficiaries, and rapidly move funds out through instant-payment rails or crypto exchanges. By the time the genuine customer notices, the funds are gone, and the trail has been obfuscated.
Explore key fraud statistics, regulatory shifts, and actionable recommendations from Veriff’s new report.
Best ways to prevent account takeover fraud in online banking
Preventing ATO in digital banking requires a layered, risk-based approach. There’s no silver bullet – only a combination of controls, processes, and continuous improvement. Here’s the approach I recommend and have implemented with teams across regions.
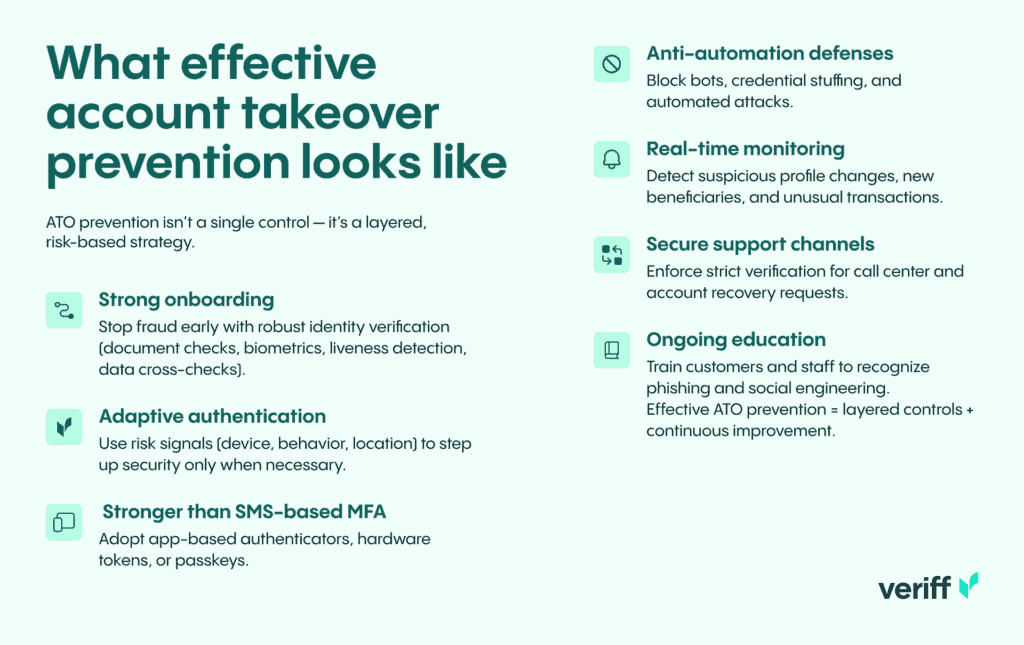
1. Strengthen identity verification at onboarding. Stopping fraud before it becomes an account is the most cost-effective control. Strong digital identity verification – document checks, liveness detection, biometric matching, and data cross-checks – reduces the risk that fraudsters will open new accounts with stolen or synthetic identities.
2. Apply adaptive, risk-based authentication. Rather than relying solely on static MFA, use contextual signals – device reputation, IP/geolocation anomalies, behavioral biometrics, and transaction risk scoring – to step up authentication only when risk rises. This approach reduces friction for genuine users while making attacks harder and more costly for fraudsters.
3. Move beyond SMS-based MFA. SMS one-time codes are vulnerable to SIM swap and interception. NIST and industry leaders recommend stronger authentication methods – app-based authenticators, hardware tokens, or standards-based cryptographic approaches such as passkeys – to reduce account takeover risks.
4. Detect and block automated credential attacks. Implement anti-automation defenses: bot management, rate limiting, device fingerprinting, and credential stuffing detection. These controls need continuous tuning to keep pace with rapidly evolving attack techniques.
5. Monitor for account takeover indicators. Real-time monitoring that looks for rapid profile changes (email, phone, address), unusual beneficiary additions, or atypical transaction patterns enables early detection and automated containment such as transaction holds or forced re-authentication.
6. Tighten call-center and support workflows. Social engineers often exploit weak customer service authentication to reset credentials. Enforce strict, multi-factor verification for any account changes requested through support channels and log all such interactions for review.
7. Educate customers and staff. Awareness reduces successful phishing and social engineering. Regular, targeted communications and simulated phishing exercises for staff help raise the cost of attacks for fraudsters.
Balancing security and customer experience
I frequently hear the question: ‘How do we protect customers without making our product unusable?’ The answer is by being intelligent about when and how we apply friction. Risk-based authentication and progressive profiling let you keep onboarding and day-to-day banking smooth for most users, while applying stricter verification when risk signals spike. Communicate transparently with customers: if you’re about to step up verification, tell them why – customers are more tolerant of friction when they understand it’s protecting their money.
Operationalizing prevention: technology and governance
From my experience, success requires integration across technology stacks and governance structures:
Centralized identity and fraud telemetry. Aggregate signals from onboarding, authentication, transactions, and customer support into a centralized fraud platform. Correlating signals across channels improves detection and reduces false positives.
Cross-functional playbooks and incident response. Fraud teams, legal, compliance, and customer operations must have pre-approved response playbooks for suspected ATOs so you can contain, investigate, and remediate quickly and consistently.
Regulatory alignment and reporting. Ensure your controls comply with regional regulations on authentication, customer notification, and data protection. Proactive engagement with regulators and auditors helps avoid surprises during reviews.
Measuring success and staying ahead
Key performance indicators matter. Track metrics like successful ATO attempts blocked, time-to-detection, funds recovered, false-positive rates, and customer friction metrics (drop-off at onboarding, authentication abandonment). Continuous monitoring and iterative improvement are essential – attackers continuously adapt, so your defenses must, too.
Case studies and real-world outcomes
Over the years I’ve worked with banks that reduced ATO losses substantially by combining stronger identity verification at onboarding with risk-based authentication. One client implemented device reputation and behavioral analytics alongside mandatory app-based authenticators for high-risk actions. Within months their ATO incidents attributable to credential stuffing fell dramatically, and customer complaints about fraud decreased.
Another financial institution reworked its call-center authentication and added a secondary verification channel before processing beneficiary changes. This simple governance change cut the number of social-engineering-based account changes by more than half in the first quarter after rollout.
Practical checklist: immediate steps you can take
If you’re responsible for compliance, risk, or fraud, here’s a pragmatic checklist you can act on this month:
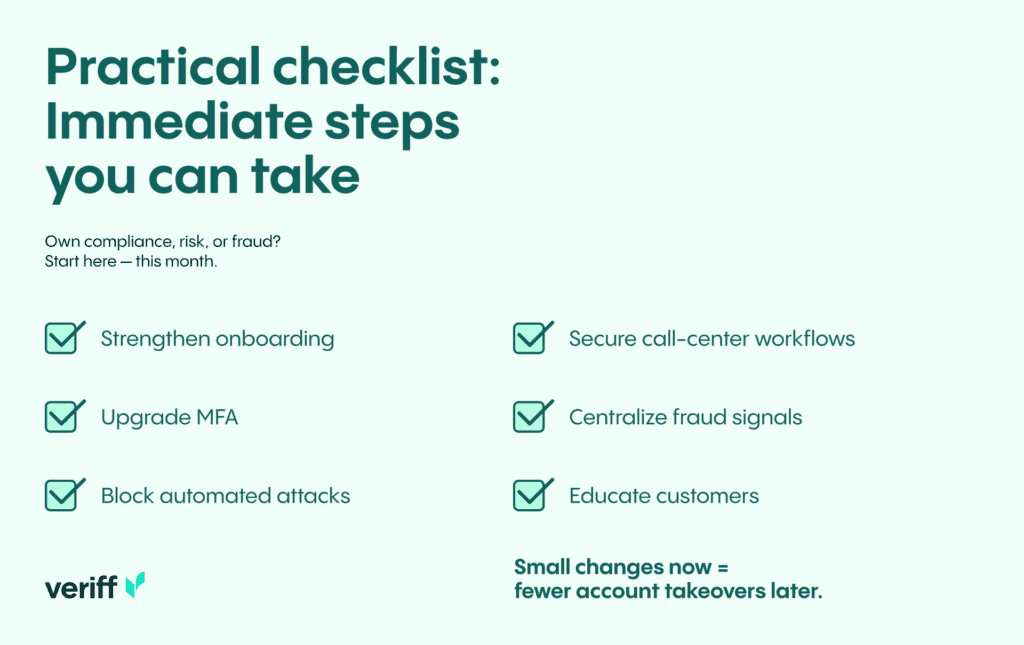
- Review and strengthen onboarding identity verification. Add document verification and liveness checks where risk warrants.
- Replace or complement SMS-based MFA with stronger authenticator options or passkeys.
- Implement bot and credential-stuffing defenses on login and API endpoints.
- Audit call-center authentication procedures and enforce multi-factor verification for account changes.
- Centralize fraud telemetry and run targeted analytics to detect early ATO indicators.
- Run customer education campaigns about phishing and password hygiene.
Why identity verification technology is central to prevention
In my view, identity verification is the foundation of account takeover prevention. If you can reliably and frictionlessly confirm that an individual is who they claim to be at onboarding and during high-risk actions, you reduce the attack surface dramatically. Modern identity platforms combine document proofing, biometric checks, and data-driven fraud signals to make that verification robust and automated – so you can scale protection across millions of customers without burdening genuine users.
Final thoughts: urgency and opportunity
Account takeover fraud isn’t an abstract risk – it’s a present, growing threat that targets customers and institutions across geographies. I want to be candid: if you treat ATO as a checkbox rather than a continuous strategic priority, you’ll be reacting to losses instead of preventing them. The good news is that practical, proven defenses exist. By combining stronger identity verification, risk-based authentication, anti-automation controls, and operational governance, you can dramatically reduce ATO risk while maintaining a positive customer experience.
Protect your customers from account takeover – strengthen your identity verification with Veriff.
