IDV Article
Navigating compliance: Identity Verification checklist and how to file a suspicious activity report (SAR)
Complying with AML laws isn’t just a legal box to check—it’s vital for protecting your business, customers, and the financial system. Whether you’re a startup, SMB, or established institution, the right tools and processes are key to staying compliant and reducing fraud risks.
For financial service providers, compliance with Know-Your-Customer (KYC) regulations and anti-money laundering (AML) laws is critical. It´s not just about meeting legal obligations but also about protecting your business, customers, and the financial system. Whether you’re a startup, small-to-medium-sized business (SMB), or an established institution, having the right tools and processes can make all the difference in staying compliant and reducing fraud risks.
To help you navigate these challenges, we’ve created two essential resources:
- The Identity Verification compliance checklist
- The employee guide: How to file a suspicious activity report (SAR)
These guides are designed to provide actionable steps for building a robust compliance framework, equipping your team to identify and report suspicious activity, and assisting you to protect your business from financial crime. Let’s dive into what each resource offers and how they can help.
Resource 1: Identity Verification checklist
The Identity Verification compliance checklist is a practical guide tailored for startups, SMBs, and compliance leaders in financial services. It outlines the key steps to streamline identity verification (IDV) workflows, minimize fraud risks, and safeguard sensitive customer data—all while assisting your compliance posture.
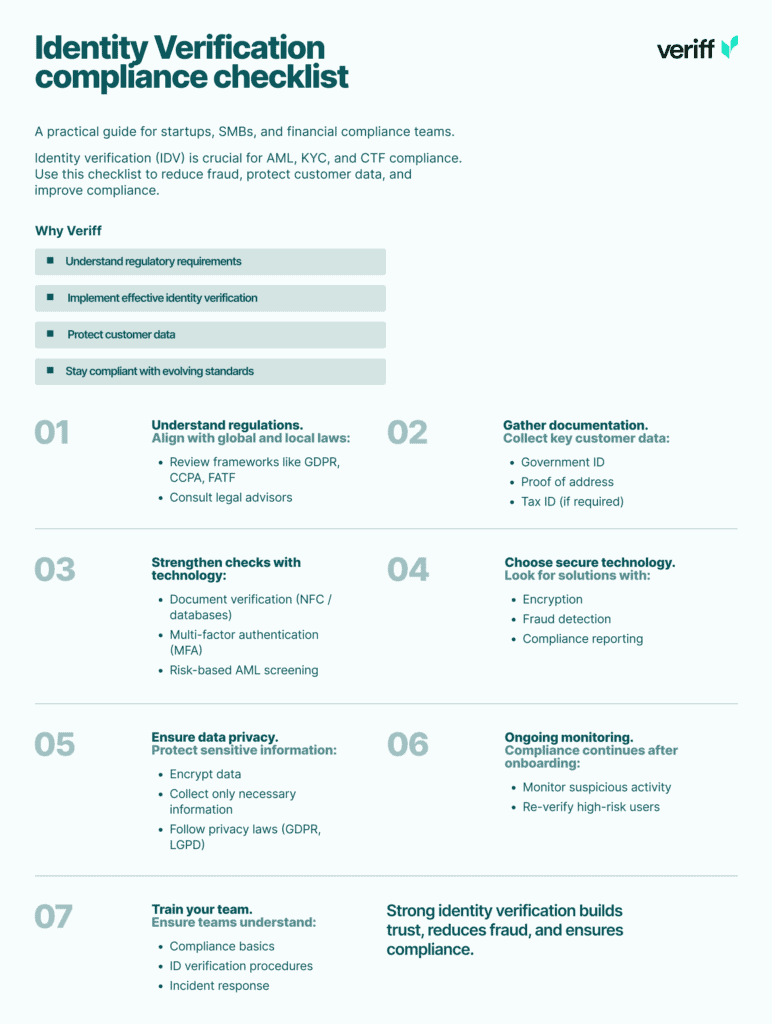
Why you need this checklist
For financial service providers, identity verification is the foundation of compliance with AML, KYC, and CTF regulations, which can be complex for businesses operating globally. This checklist simplifies the process, providing a clear roadmap to help you:
- Understand the nature of regulatory requirements.
- Implement effective IDV methods.
- Protect customer data.
- Keep up the pace of evolving compliance standards.
What’s inside the checklist?
1. Understand regulatory requirements
- Familiarize yourself with landmark laws, including GDPR, CCPA, FATF, and more.
- Consult legal advisors to ensure your practices align with local applicable regulations.
2. Gather required documentation
- Collect government-issued IDs, proof of address, and tax identification numbers, as required under applicable AML/KYC laws.
- Use biometric verification (e.g., selfies with liveness detection) to confirm identities and prevent fraud.
- Where necessary, also implement specific KYC methods that are required in the country where you are licensed.
3. Implement verification methods
- Leverage tools like NFC and validate against authoritative document reference databases for document verification.
- Use multi-factor authentication (MFA) for verified users and implement additional risk-based AML measures for higher-risk users to strengthen security.
4. Choose proven software and technology
- Invest in scalable IDV solutions with advanced encryption, fraud detection, and reporting capabilities.
5. Ensure comprehensive data privacy measures
- Encrypt sensitive data, minimize data collection, and comply with applicable privacy laws, whether GDPR, LGPD, or your local applicable privacy law.
6. Ongoing monitoring and risk assessment
- Continuously monitor your users for suspicious activities and re-verify high-risk customers periodically.
7. Train your team
- Provide employees with training on compliance basics, IDV procedures, and incident management protocols.
Download the Identity Verification compliance checklist to streamline your IDV workflows and strengthen your compliance posture.
Try for Free
Start your 15-day free trial — No credit card needed.
Explore Veriff’s Self-Serve Plans with Transparent Pricing and Powerful Feature
Resource 2: Employee guide: How to file a suspicious activity report (SAR)
Your employees are your first line of defense against financial crime. The employee guide: How to file a suspicious activity report (SAR) equips your team with the knowledge and tools they need to identify and report suspicious activity effectively, a quintessential part of your compliance with AML regulations.
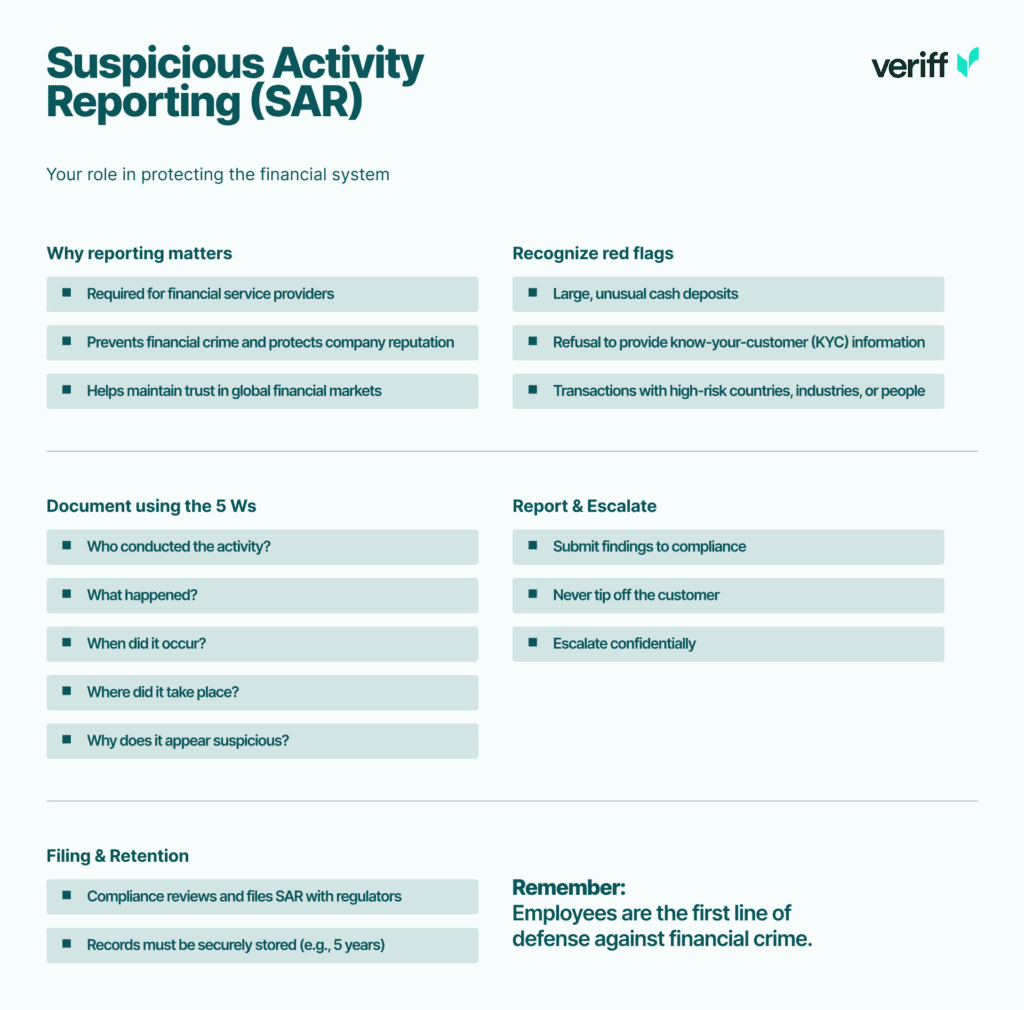
Why this guide matters
Filing a suspicious activity report (SAR) is a legal obligation for financial service providers in most jurisdictions. Failure to report suspicious activity can lead to severe penalties, reputational damage, and even criminal liability. This guide ensures your employees understand their role in detecting, documenting, and reporting suspicious activity.
What’s inside the guide?
1. Understand why reporting matters
- Helps to protect your company from financial crimes, reputational damage, and regulatory penalties.
- Safeguards the integrity of and trust in global financial markets.
2. Recognize red flags
- Examples of suspicious activity include:
- Large cash deposits inconsistent with the customer’s established behaviour on your platform (customer profile).
- Reluctance to provide requested information needed for your KYC processes or vague explanations about the source of funds.
- Transactions involving high-risk individuals, countries or industries.
3. Document and report
- Use the “5 Ws” framework to document suspicious activity:
- Who: Who conducted the activity?
- What: What was the activity?
- When: When did it occur?
- Where: Where did it happen?
- Why: Why did it seem suspicious?
- Submit your findings to your company’s compliance officer or designated team.
4. Review and escalate
- Do not disclose the investigation to the suspect or “tip off” the user, as this is a criminal offense in most jurisdictions.
- Escalate your findings securely and confidentially to the appropriate compliance team.
5. Filing and retention
- Compliance officers will assess the report and, where relevant, file it with the appropriate regulatory authority.
- All records related to the SAR must be securely stored for a minimum period as required under the law (e.g., 5 years).
Download the Employee guide: How to file a suspicious activity report (SAR) to equip your team with the knowledge they will benefit from to identify and report suspicious activity effectively.

How these resources work together
The Identity Verification compliance checklist and the Employee guide: How to file a suspicious activity report (SAR) are complementary tools that address two critical aspects of compliance:
- Building a strong compliance framework
The checklist provides a step-by-step roadmap for implementing effective IDV processes, ensuring your business activities align with applicable compliance standards. - Empowering your team to act
The SAR guide equips your employees with the knowledge and framework to identify and report suspicious activity, ensuring your business can stay compliant and protected.
Together, these resources help financial service providers create a culture of compliance, reduce fraud risks, and safeguard their operations.
Take the next step: Download the guides!
Compliance doesn’t have to be overwhelming. With the right resources and tools, financial service providers can build a strong compliance framework that protects their business and customers.
To streamline your IDV workflows and strengthen your compliance posture:
To equip your team with the knowledge they need to identify and report suspicious activity effectively:
By leveraging these resources, you can simplify compliance, reduce fraud risks, and build trust with your customers.
Disclosure
This blog is for informational purposes only and does not constitute legal advice. Financial service providers should consult qualified legal counsel to ensure compliance with applicable laws and regulations in the jurisdictions where they operate.

