IDV Article
Stop taking fraud lightly: Granting Veriff data controllership for superior fraud prevention
Granting Veriff data controllership isn’t just a legal checkbox — it’s a strategic decision that unlocks the machine learning flywheel needed to outpace modern fraud. In this deep dive, we explore how enabling Veriff to process data for model training and development strengthens fraud prevention systems, accelerates detection of emerging attack patterns, and ultimately helps organizations stay ahead in the escalating fraud arms race.
Fraud has evolved beyond simple opportunistic attacks into a sophisticated, coordinated threat vector. Static, rules-based defenses are no longer sufficient against adversarial machine learning and organized fraud rings. To effectively combat modern fraud, technical leadership must shift from reactive containment to proactive fraud prevention strategies fueled by dynamic data and continuously retrained machine learning models.
For organizations leveraging identity verification (IDV), allowing your provider to process data for training and development purposes is not merely a legal nuance. It is a critical architectural decision.
This technical deep dive explores why granting Veriff data controllership is the mechanism that powers the machine learning flywheel necessary to stay ahead of emerging threats.
The core technical imperative: The machine learning flywheel
At the heart of superior fraud prevention lies the data feedback loop.
In a standard “Processor-only” engagement, data usage is restricted, creating silos that prevent machine learning models from accessing diverse, real-world training data they need to perform effectively.
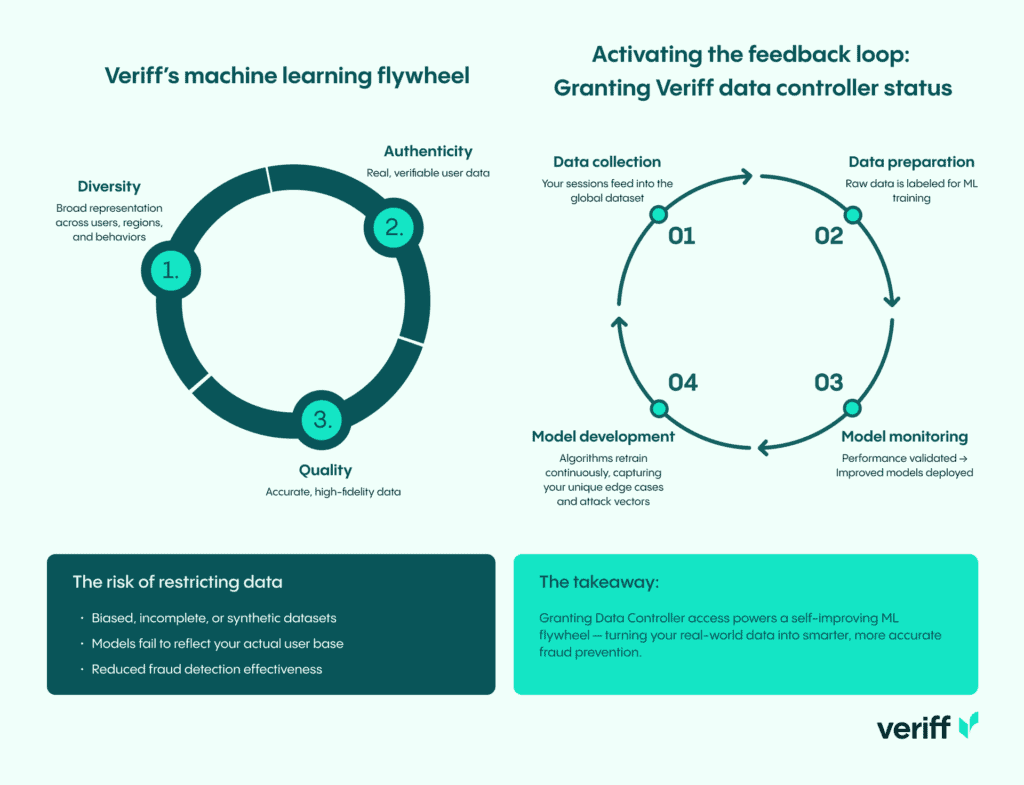
Data is the foundation of all ML endeavors. Veriff’s core development flywheel is built on three data pillars: diversity, authenticity, and quality.
When you grant Veriff Data Controller status, you activate a powerful feedback loop:
- Data collection: Sessions from your specific traffic contribute to the global dataset.
- Data preparation: Raw data is labeled.
- Model development: Algorithms are continuously retrained on this broader dataset, capturing edge cases or attack vectors specific to your use case, industry, or region.
- Model monitoring: Performance is validated, and the improved models are deployed.
Biased, unrepresentative, or incomplete datasets compromise results. Restricting data use by requiring a pure Data Processor role forces Veriff to depend on synthetic or unrepresentative datasets to train its models, which fail to capture the specific characteristics of your user base. Assigning Veriff Data Controller status ensures our fraud detection models are trained on precise, relevant traffic, delivering more accurate and reliable verification outcomes.
Measurable performance gains: The “Network Effect” of security
The performance gains obtained by granting Veriff Controller status are not theoretical. Such a change yields quantifiable optimizations across your verification funnel. By leveraging Veriff’s core development cycle, organizations see immediate improvements in accuracy.
Our data shows that customers who enable Veriff to act as an independent controller achieve significantly better outcomes than processor-only setups — delivering up to 50% higher fraud detection at no measurable impact on false rejections, strengthening protection against advanced attacks.

Our data shows that customers who enable Veriff to act as an independent controller achieve significantly better outcomes than processor-only setups — delivering up to 50% higher fraud detection at no measurable impact on false rejections, strengthening protection against advanced attacks.

Case study: Large mobility company
Consider the case of a major mobility provider. Initially, one of our new models underperformed because their specific traffic data hadn’t been used in the training set. The “domain gap” between generic training data and their real-world environment was too wide.
Once their data was included in the model training, we closed that loop. The result?
- Improved document fraud and face fraud detection.
- +10% additional fraud cases caught without any increase in false rejections.
Addressing the misconceptions: Ownership and privacy
Legal and InfoSec teams often cite concerns over data sovereignty as a primary friction point. It is essential to address the technical and legal frameworks governing this relationship with precision.
Granting data controllership to Veriff is strictly limited to processing permissions defined under “Permitted Business Purposes” in the Data Processing Agreement (DPA). You are authorizing Veriff to utilize data for the specific purpose of training machine learning models to enhance identity verification performance and fraud detection.
Privacy-preserving ML architecture
Our ML training pipeline is built on privacy-by-design principles, with privacy safeguards embedded at every stage of development.
Pattern-based learning
Our models are trained on real-world verification data, like document images and biometric features, to recognize general fraud patterns and signs of authenticity. The goal is to learn statistical signals of fraud and legitimacy from large, diverse datasets. For instance, a model learns what makes up “a forged French ID” or “a printed face attack” from thousands of examples, rather than storing information about one person.
Statistical representation, not data storage
Once trained, models only contain learned statistical patterns encoded in parameters. Model outputs, such as fraud risk scores or liveness assessments, are based on patterns learned across millions of sessions. Individual training examples cannot be retrieved from the trained model.
Purpose limitation
Data is processed solely for product development and quality assurance purposes. It is never sold or used for unrelated commercial activities.
Security posture: ISO, SOC, and GDPR
Granting controller status does not degrade your security posture. The legal distinction between Processor and Controller does not weaken the rigorous technical controls we apply to data at rest or in transit.
- Compliance: Veriff maintains full compliance with GDPR, CCPA, and other global regulations. We are ISO 27001 certified and AICPA SOC compliant.
- Access control: Internal access is governed by the principle of least privilege. Even for human-in-the-loop review, data is accessed in secure, controlled environments with strict audit logging.
The technical verdict
Fraudsters operate collaboratively, sharing tools, exploits, and stolen identities. Your defense strategy must be just as interconnected.
By maintaining a “Processor-only” relationship with Veriff, you limit access to network-wide learnings derived from multiple controllers, potentially leaving fraud detection performance and accuracy improvements on the table in a rapidly evolving threat landscape.
Granting data controllership to Veriff is the strategic choice to leverage a dynamic, self-reinforcing fraud prevention framework. This simple adjustment, often requiring just a written update to the DPA, delivers significant benefits: reduced response times, increased conversion rates, and stronger protection against emerging fraud threats.
Ready to upgrade your fraud defense? Contact Veriff to initiate the controller amendment process.
