Fraud Article
How Veriff keeps your personal data safe
In a digital world where identities are forged and trust is fragile, we believe your personal data should never be the weak link. At Veriff, protecting your information is not just part of our service — it’s our promise. Here’s how we safeguard your data at every turn, so you can feel confident about who you are online and how you’re verified.
Veriff is an identity verification company entrusted with large amounts of personal data. We take this responsibility seriously and are transparent about our security practices.
In this article, we explain the robust measures we use to protect your personal information at every stage of the identity verification process.
Why is secure Identity Verification important?
Secure identity verification is essential for building trust in the digital world. With online fraud on the rise, businesses and individuals need assurance that their data is protected. Veriff provides this assurance through a commitment to security, compliance, and privacy-first principles.
Rising fraud threats: According to the Veriff Identity Fraud Report 2025, fraudulent activity surged by more than 20% in 2024 alone. Among these cases, impersonation fraud made up a staggering 82%, underscoring the increasing sophistication of cybercriminal tactics. Meanwhile, account takeover incidents grew by 13%, and multi-accounting cases rose by 10% compared to the previous year.
Sophisticated tactics: Impersonation fraud accounts for 82% of cases, highlighting the need for advanced defense mechanisms.
Compliance: Veriff adheres to major data protection frameworks like GDPR in Europe, CCPA in the US, and LGPD in Brazil, ensuring your rights are protected.
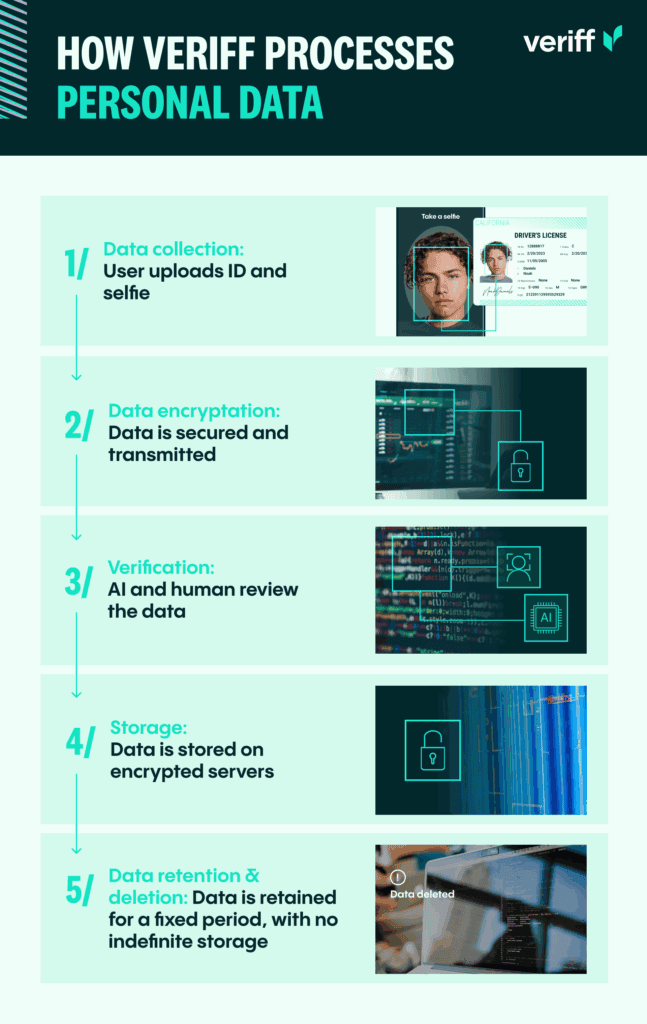
How does Veriff process personal data?
Veriff processes personal data to perform identity verification on behalf of our business customers. We act as a data processor, which means the company that asks you to verify your identity determines the purpose of the data processing.
Your rights. Veriff recognizes every individual going through its verification flow as a data subject. The data subject is always in the center of Veriff’s service. You as the data subject, are entitled to specific information and the exercise of data privacy rights. That is why Veriff makes it clear in its Privacy Notice that Veriff is providing its verification services to other companies. Veriff collects your data via its verification service only if you have been directed there by a business customer of Veriff. Veriff’s customer, the company asking you to verify your identity, decides how and for which purposes Veriff processes your data. This also means they must tell you how they and Veriff process your data, and ensure you can exercise your rights along the way.
Veriff’s services process personal data. The EU’s General Data Protection Regulation (known as GDPR) defines personal data as any information about an individual who can be identified, directly or indirectly, by name, ID number, or other factors relating to an individual’s physical, physiological, genetic, mental, economic, cultural, or social identity. The data collected by Veriff for your identification is personal data and Veriff’s customers must ensure that they have a valid legal basis for allowing Veriff to use the data for its services.
What are your rights as a data subject?
As a data subject, you have specific rights regarding your information. The business that directed you to Veriff is responsible for informing you how your data is used and how you can exercise your rights. Our Privacy Notice provides clear information on our role and responsibilities.
What kind of data does Veriff process?
Veriff processes the personal data needed for identification, which can include your name, ID number, and images of your face and identity documents. This may include biometric data, a type of sensitive information that requires stricter legal protections but provides a strong layer of security against fraud.
How do we protect your data?
Veriff employs a multi-layered security strategy to safeguard your data. This includes proactive risk management, advanced technical measures, and strict internal policies. Our approach is built on a “security by design” philosophy that integrates protection into every aspect of our service.
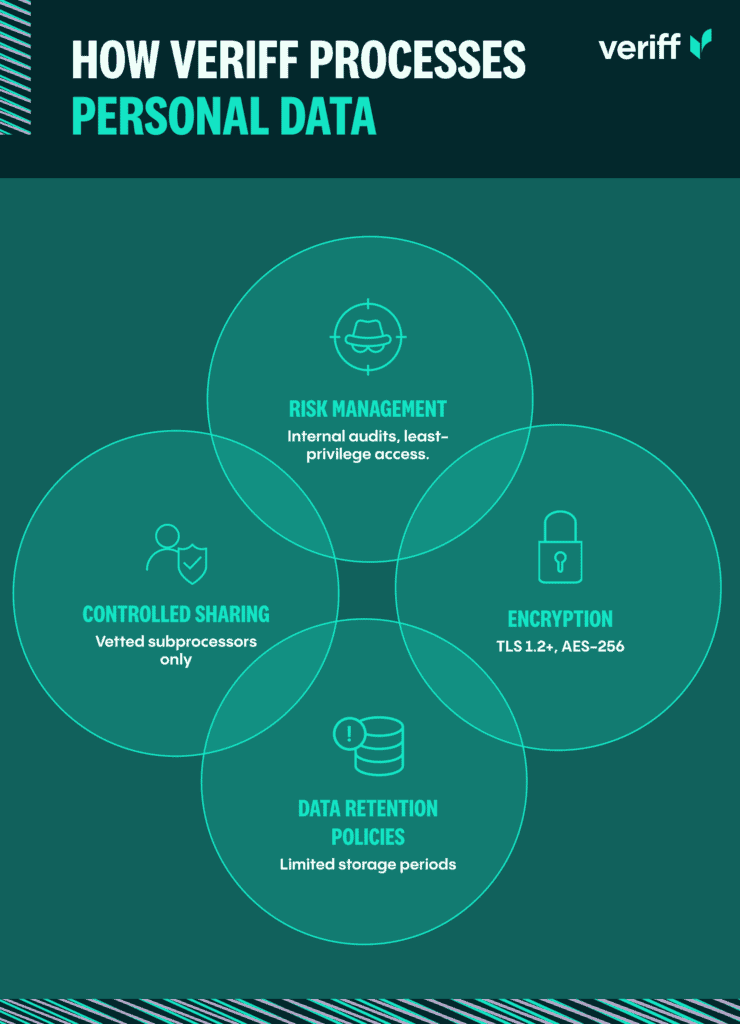
Dedicated risk management
Our privacy and compliance teams conduct regular data protection impact assessments. This approach helps us proactively identify and mitigate risks associated with our identity verification solutions. We ensure data access is granted on a least-privilege basis, meaning employees can only view information essential for their roles.
These data protection impact assessments not only fulfill legal requirements but also allow Veriff to proactively identify and address the risks related to our products and services. By leveraging our in-house legal competence and taking proactive information security measures—such as employing multi-factor authentication and advising on password manager use—Veriff ensures the highest level of data security to uphold our commitment to safeguarding your privacy and protect your data.
No selling or unauthorised sharing of end user data
As stated in Veriff’s Privacy Notice, we’ll disclose your personal data to the customer who has authorized us to provide you with the identity verification service. Additionally, as an integral part of the identity verification service, your personal information may be disclosed to our carefully chosen sub-processors. These are service providers helping us with different data processing and cloud storage services, being essential to providing our identity verification service. Internally, any access to data is granted on a need-to-know and least-privilege basis. This means that our employees are only granted the information and access rights strictly necessary for their specific tasks—helping prevent insider threats and ensuring your data remain safe from internal and external compromise. This ensures your data is always kept safe with no unauthorized access.
Defined data storage periods
The term for keeping your data is fixed in internal policies and customer agreements. Veriff never keeps data indefinitely. For example, as a standard, personal data which is processed on behalf of our customers is stored for no longer than 3 years. However, in the context of identity verification services, this may differ depending on the customer’s instructions. That is why the company that asked for your identity verification is the one that can tell you the exact time for how long your data is stored and used for identity verification. Storing your data only as long as necessary is an essential security measure to help keep your data secure and reduce risks such as exposure through social media leaks or legacy systems.
Encryption at rest and in-transit
In Veriff, data is encrypted both at rest and in transit. Encryption is the process of converting data into an unreadable format, making it inaccessible to the user who does not have the decryption key. Encryption enables secure and confidential end-to-end protection of the data by protecting its content.
Encryption is a core component of our data security. Veriff uses strong encryption protocols to protect your data at all times. Data in transit is encrypted using Transport Layer Security (TLS) 1.2 or a newer version.
– Data in transit is encrypted using Transport Layer Security (TLS) 1.2 or higher, securing data as it moves over the internet.
– Data at rest is encrypted using Advanced Encryption Standard (AES-256), a globally recognized standard.
In addition, all internal applications hosted by Veriff and used to manage personal information are also channeled into VPN as an extra measure to reduce the attack surface and to provide an additional layer of security around the standard TLS. These practices help ensure your data is not compromised via WiFi network vulnerabilities or phishing emails.
What are Veriff’s security certifications?
Veriff’s commitment to security is proven by independent, internationally recognized reports and certifications. These documents confirm that our systems and processes meet the highest standards for data protection and information security.
– SOC 2 Type 2: This is an independent third-party examination that demonstrates how well Veriff’s security controls operate over a year.
– ISO/IEC 27001:2022: An international standard for information security management system (ISMS), validating our systematic, risk-based approach to continually manage and protect assets.
– UK Cyber Essentials: This UK government-backed scheme certifies our defenses against common cyber threats. the UK’s Cyber Essentials scheme is designed to help protect organizations against a whole range of the most common cyber attacks.
You can learn more about the Cyber Essentials from the UK’s National Cyber Security Centre’s webpage. These security measures are just some examples that are put in place here in Veriff. We take all necessary precautions to give you peace of mind when using our identity verification service—even in your day-to-day interactions online. We always follow the relevant updates and implement additional measures to ensure compliance.
Want to dive deeper?
Learn more about our security practices on our Security and Compliance
How Valr protects users and data while scaling fast with Veriff
When Valr — a global crypto exchange with more than one million users — set out to scale rapidly while navigating an evolving regulatory and fraud-landscape, they turned to Veriff for a solution that would keep their onboarding friction low and their data and users protected. As Valr’s Compliance Manager puts it: “We needed something intelligent and constantly evolving … the crypto world moves fast and is a constant target for fraud.”
Veriff’s advanced identity verification platform, with biometric and liveness checks, wide document-set coverage (particularly for Africa), and strong integration support, gave Valr the confidence to grow aggressively without sacrificing compliance or user trust.
The result: Valr could launch growth campaigns, bring in thousands of new users in a single day, and rest assured that behind the scenes, data was being handled rigorously, fraudsters blocked, and real users onboarded seamlessly.
Securing the digital world: Veriff’s vision for a safer, trust-first future
At Veriff, we know that fraud doesn’t stand still—so neither can we. As identity threats grow more sophisticated—from biometric deepfakes and AI-generated impersonations to evolving social engineering tactics—Veriff is at the forefront, proactively safeguarding the digital world. We don’t wait for tomorrow’s risks to arrive—we anticipate them.
Our commitment begins with cutting-edge technology. Veriff continuously evolves its trust infrastructure, supported by AI models, real-time risk analysis, and advanced threat detection systems. But technology alone isn’t enough. True digital safety requires a broader vision.
That’s why we go further—collaborating with regulators, contributing to global trust frameworks, and partnering with industry leaders to shape a secure and trustworthy digital landscape. Because for us, building trust online isn’t optional—it’s essential.
Trust is also about privacy and compliance. Veriff aligns its data protection practices with leading global standards, including the European Union’s General Data Protection Regulation (GDPR), while staying agile amid emerging frameworks such as the EU’s AI Act.
Looking ahead, Veriff’s vision is clear: a world where individuals move freely and securely through digital spaces—supported by identity verification that is seamless, privacy-first, and globally scalable.
We’re not just responding to the threats of today. We’re shaping the internet of tomorrow—one where trust fuels progress and people come first.
Frequently Asked Questions (FAQ)
1. Does Veriff sell my data?
No, Veriff never sells your personal data. We only share your information with the company that requested your identity verification and with essential service providers who are part of our secure verification process.
2. How long does Veriff keep my data?
Veriff stores personal data for a fixed period and is typically no longer than three years. We never store personal data indefinitely.
3. What is biometric data and why does Veriff process it?
Biometric data refers to information about your unique physical characteristics, like your facial features. Veriff processes it to uniquely identify you and provide a strong layer of security against impersonation fraud.
4. How is my data kept safe during transfer?
Your data is encrypted both in transit (while it travels over the internet) and at rest (when it is stored). We use industry-standard protocols like TLS 1.2 and AES-256 encryption to ensure its confidentiality and integrity.
5. Who is responsible for my data?
The company that asked you to verify your identity is the data controller, meaning they decide the purposes and means of processing your data. For the purposes of the service, Veriff acts as the data processor, carrying out the verification securely on their behalf.

